SQL Injection
It is a way of hacking on a database driven application in which the hacker executes unauthorized SQL commands by taking advantage of insecure code on a system connected to the Internet, bypassing the firewall.
SQL injection hackers are used to steal information from a database from which the data would normally not be available and/or to gain access to an organization’s host computers through the computer that is hosting the database.
SQL injection attacks typically are easy to avoid by ensuring that a system has strong input validation.
Example:
This is your query when the user clicks on a Login button in your system
Select [UserName], [Password] From Users Where UserID = 1;
Here is what the hacker would type in the input fields like username textbox:
Select [UserName], [Password] From Users Where UserID = 1; Drop Table Users;
Never use a direct query from your application to database.
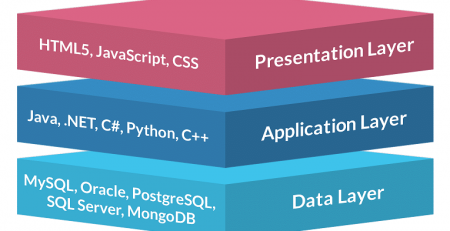
Instead use web services or stored procedures and implement layers such as data access layer and business logic layer, this would protected you against SQL injection.







Comments (8)
ma shaa Allah, jazakum Allahu khayran 🙂 loved the post, simple enough.
Thanks Amr
if I insist to use simple queries , is there a work around to not be injected?
The only work around that I can think of is to remove all the special characters that you might have in your query. Still I don’t recommend that.
Nice post!
There is a way to use direct SQL commands without using stored procedures, if you are using asp.net, wrap your query variable in SQL Parameter.
If you are using PHP, wrap your query variable in function mysql_escape_string.
This simply converts harmful chars to non harmful chars..
I have read so many posts concerning the blogger lovers however this article is truly a pleasant paragraph, keep it up.
It’s a pity you don’t have a donate button! I’d certainly donate to this superb blog! I suppose for now I’ll settle for book-marking and adding your RSS feed to my Google account. I look forward to new updates and will talk about this site with my Facebook group. Talk soon!